This tab is dedicated to the file tracking capabilities of this program. Unlike the previous version of this program, which would show you only tracked programs and would only allow you to track all programs on your device, this utility allows you to see a list of all programs on your device and to individually choose which files to track. This program indexes all mass-storage filetypes on your device... programs and appvars.
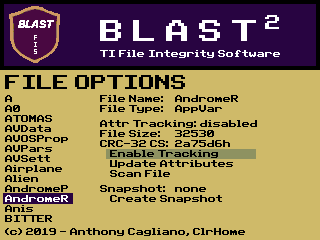
On the lefthand side of the screen, you will see a list of all the variables found on your device. You may scroll through this list by using the ↑ or ↓ keys. Sometimes, however, you may find the need to scroll through files in bulk. Use the ← and → keys to jump from one page worth of files to the next.
The interface for file manipulation is fairly simple once you figure it out. Basic information about the file is presented... its name, type, size, CRC-32 checksum, and the timestamp of the last saved snapsshot (if one exists). There are also several menu items available for doing things with your files: Enable Tracking, Update Attributes, and Scan File within the Attributes section and Create or Update Snapshot within the Snapshot section (click on the Snapshots tab for more on that). You can use the Enter key with a file selected to access menu options for that file as well as to select a selected option. Use the Clear key to go back or to move out of any menu you are currently in. Use the ↑ or ↓ keys to move between menu options.
File Integrity Functions
Turning on attributes tracking for a file adds the current size, type, and CRC-32 checksum to a database. Once this option is enabled, any time you view the file in the File Options menu, you will see either a green icon or a red icon, indicating whether the file's attributes have changed since the last time they were saved. Also, once you have turned on tracking for a file, the "Enable Tracking" menu item changes to "Disable Tracking", which allows you to disable tracking on the file. The "Update Tracking" option allows you to resave new attributes for a tracked file.
 In addition to monitoring changes to a file, this program also has very basic malware detection capabilities. There is a community-sourced malware definitions file available for download for use with this program. It contains a database of potentially harmful strings of code. You may scan a file (or the operating system) using this database by using the "Scan" option. See the example of a file being scanned. For some obfuscation, the program no longer displays the actual code being checked for. Instead it displays a code name selected by the person who submits the definition (you can see the associated malware string and description on the Malware Definitions tab of this page). In the event that a match for a malware string occurs, you are told the address at which this match occurs. When the scan is complete, the program prints "Done!"
In addition to monitoring changes to a file, this program also has very basic malware detection capabilities. There is a community-sourced malware definitions file available for download for use with this program. It contains a database of potentially harmful strings of code. You may scan a file (or the operating system) using this database by using the "Scan" option. See the example of a file being scanned. For some obfuscation, the program no longer displays the actual code being checked for. Instead it displays a code name selected by the person who submits the definition (you can see the associated malware string and description on the Malware Definitions tab of this page). In the event that a match for a malware string occurs, you are told the address at which this match occurs. When the scan is complete, the program prints "Done!"